Why Remove Administrator Privileges?
Editor’s Note: This article was published in 2017 and has been updated for accuracy and comprehensiveness as of November 2020.
If a user didn’t have administrator privileges in the era of Windows XP, they couldn’t do anything on the computer. So much so that nothing could be done on the computer besides word processing, using a calculator, and maybe MS Paint. It was painful, to say the least. Nowadays, having administrative rights is the most dangerous thing about using a Windows operating system. Thankfully, Microsoft has made it possible for us to fix this.
What’s the big deal?
It’s important to understand the actual vulnerabilities that are in place when your user account has the most powerful permissions available. Sure, you can install programs at will, but how often do you actually have to do that once the system is working and running as you want? Having these elevated permissions means that anytime you encounter an infected website or preview an infected email, the malicious code that attempts to run behind the scenes also gains access to your elevated permissions to the entire system, allowing it to do whatever it wants. Your registry, your file system, even your files are all free for the taking.
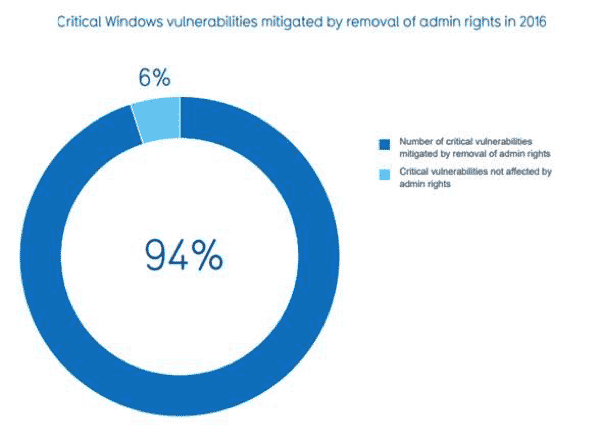
There is plenty of research to back up this theory that has been performed by numerous security companies. For instance, Beyond Trust’s 2016 Microsoft vulnerabilities survey found 416 vulnerabilities present in desktop operating systems newer than Vista up to Windows 10. When they removed admin rights, here is what they found:
This study found that removing administrator privileges mitigated 94 percent of these vulnerabilities.
Additionally, removing privileges mitigated vulnerabilities in Internet Explorer, Microsoft’s Edge browser, and Microsoft Office 100 percent of the time. By simply removing administrative privileges, all 109 vulnerabilities in those applications are remediated. That sounds like more protection than the strongest firewall to me.
I need administrator rights to do my job.
In days past, you probably did. There are still some special cases where this is true. However, these myths have been busted in recent years. With a little attention to detail, we can make the end-user experience just as good as it’s ever been, not to mention more safe and secure.
Here are some of the most common excuses from IT admins and end-users alike:
Mobile users need it to install printers and update their software
Ever since Windows 7, users can grant access to add printers, update applications, and even connect to Wi-Fi hotspots, all without needing administrator privileges. Even more convenient, these settings can be pushed out through group policy so we can be even more granular with what access we need to provide for our remote sales team or even our executives. A simple internet search reveals plenty of articles about how to accomplish this.
Our Line of Business (LOB) application needs admin rights
The only reason an application would not be able to run without admin rights would be due to limited access to files. There are a number of simple and free tools that can determine exactly what the LOB is trying to do, and then adjust permissions accordingly.
My executive team needs administrative privileges
This one is just silly. I’d be willing to bet that if they knew the actual risks of this and were proven that their ability to perform their tasks were not changed, every single person on the executive team would give this up in order to make their organization a safer place to work.
Still on the fence?
The first time my manager told me to remove local admin privileges, I was reluctant. I thought, “This is going to be so painful for everyone, both customers and our support staff trying to help them.”
For those who don’t know me, my job as a Field Engineer takes me all over the Minneapolis and St. Paul metro area. I will often be out of the office for days at a time. I’m also performing job functions that require me to run commands and test out software for clients. I set up a local admin account on my computer because I thought I wasn’t going to be able to do my job without it. However, to my surprise, I’ve never needed this account. I tested for 30 days without administrative rights and waited to be proved right. Now I’m 100% convinced removing administrative rights is the way to go. I feel much more confident and will not be at risk when plugging into numerous networks throughout the day. Now, even if those networks are compromised, they won’t do as much damage.
Times are changing and we can never be too secure. Removing your end-users’ local admin rights might be the most important thing to protect your network. For any questions you have about network security or administrator privileges, contact SUCCESS Computer Consulting at 763-593-3000.